WiFi In The Arena
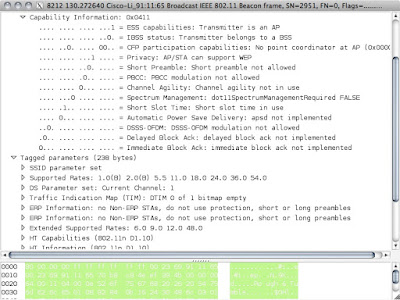
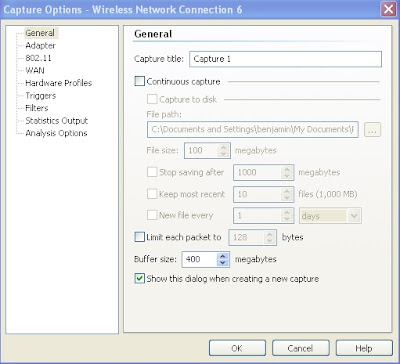
UFC 125 happened on New Year's Day, and I was fortunate enough to cover the show for the Wrestling Observer . As with just about every sporting event nowadays, the MGM Grand Garden Arena provided WiFi service for the members of the media who were covering the event. I managed to squeeze in a little bit of sniffing while I was doing my live blog , and the results I found were a little bit surprising to me. When I think of public Wi-Fi, I think of downloads. Maybe that makes me an old codger, but I just imagine all of these web pages, videos and spam emails coming down with just a few requests and acknowledgments going back up. The world has changed, of course, with more people than ever wanting to tweet, blog and upload photos as part of the social media revolution, but I still was dubious when Andrew Von Nagy ( @revolutionwifi ) told me on Twitter that I should expect a pretty even distribution of data on any public WiFi network nowadays. Sniffing in the media area turned out t...